And that’s where Fail2Ban comes in as a key security solution.
In this tutorial, we will walk you through how to use Fail2Ban to automatically scan for suspicious behaviour and ban IP addresses that make repeated failed login attempts to your MySQL database. By using Fail2Ban, you will be adding a security layer to your server that can prevent automated attacks. It’s easy to use, highly effective, and a security solution that everyone running a database on their VPS or dedicated server should have.
Why Secure MySQL?
MySQL is one of the most popular database management systems in use across the globe. It is used as a backbone for many websites, applications, and internal business systems. From e-commerce websites to content management systems, SaaS applications, and APIs, MySQL is used for storing critical information for many businesses.
However, due to its popularity, MySQL is often a victim of many cyber attacks. Malicious users often use bots that try to access MySQL servers by guessing usernames and passwords. These types of brute-force attacks often take place in the background and may continue for hours or even days.
If these attacks are not properly blocked, they can cause several issues, including:
Unauthorized Access: Attackers can access sensitive databases and obtain sensitive information.
Data Corruption or Loss: Malicious users can corrupt or delete sensitive information.
High Server Resource Usage: Continuous login attempts can cause CPU and network resource usage.
Service Downtime: Too much attack traffic can cause downtime for your database service.
Reputation Damage: A compromised database can damage the reputation of your business.
Therefore, securing MySQL should always be a priority in managing any database server.
What is Fail2Ban?
Fail2Ban is a powerful and lightweight intrusion prevention system for Linux servers. It does this by monitoring system log files for any suspicious activity, such as repeated failed login attempts or unauthorized access.
If Fail2Ban detects repeated failed login attempts from a certain IP address, it will automatically block that IP address. This will prevent hackers from continuing their attempts. This will ensure your server is protected from any brute force attacks.
Fail2Ban does this by creating something called “jails.” These are essentially services such as SSH, MySQL, FTP, or Apache. These services define conditions for banning IPs, the time for which they will be banned, and the action to take in the event that something is detected.
Since Fail2Ban is a firewall-based solution, hackers will immediately be denied access to your server. This makes Fail2Ban a very effective solution.
What Makes Fail2Ban Awesome?
Fail2Ban is widely used by system administrators because it is simple, flexible, and highly effective at protecting servers. Some of the key benefits include:
Works with Most Linux Distributions
Fail2Ban is supported on popular distributions such as Ubuntu, Debian, CentOS, AlmaLinux, and Rocky Linux.Customizable Security Rules (Jails)
You can create specific protection rules for different services, including MySQL, SSH, Apache, Nginx, and FTP servers.Automatic Firewall Integration
Fail2Ban automatically updates firewall rules using tools like iptables or firewalld to block malicious IP addresses.Real-Time Protection
It constantly monitors logs and reacts instantly when suspicious activity is detected.Email Notifications
Administrators can configure Fail2Ban to send alerts whenever an IP address is banned, helping you stay aware of potential threats.Lightweight and Efficient
Fail2Ban runs quietly in the background and uses very few system resources, making it perfect for VPS environments.
With the right configuration, Fail2Ban becomes a powerful security shield that helps protect your MySQL server from brute-force attacks and unauthorized access attempts.
What You’ll Need
Before we dive in, make sure you have:
| Requirement | Description |
|---|---|
| MySQL Installed | Running and logging properly |
| Linux Server | Debian/Ubuntu or RHEL/CentOS preferred |
| Root Access | For editing configs and installing packages |
| Fail2Ban (we’ll install it) | Protects your logs in real-time |
Pro Tip: Make sure MySQL is not exposed to the internet unless absolutely needed. If it is, then this guide is non-negotiable.
Step 1: Enable MySQL Logging
Fail2Ban works by monitoring log files. MySQL needs to log failed login attempts clearly.
On most systems:
- Edit the MySQL config:
bash
sudo nano /etc/mysql/mysql.conf.d/mysqld.cnf
- Under
[mysqld], add:
ini
log_error_verbosity = 3
- Restart MySQL:
bash
sudo systemctl restart mysql
- Trigger a failed login (on purpose):
bash
mysql -u wronguser -p
- Check logs:
bash
cat /var/log/mysql/error.log
You should see something like this:
pgsql
[Note] Access denied for user 'wronguser'@'127.0.0.1'
That’s what Fail2Ban will look for.
Step 2: Install Fail2Ban
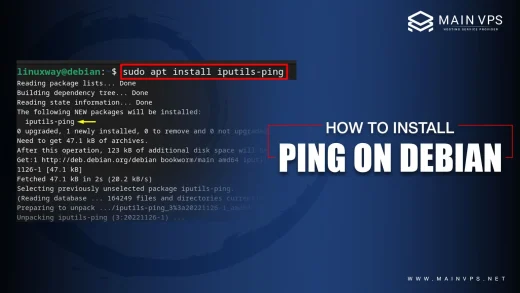
On Debian/Ubuntu:
bash
sudo apt update && sudo apt install fail2ban -y
On CentOS/RHEL:
bash sudo yum install epel-release -y sudo yum install fail2ban -y
For more, read – Mastering yum reinstall and Repository Management on CentOS
Enable and start the service:
bash
sudo systemctl enable --now fail2ban
Step 3: Configure the MySQL Jail in Fail2Ban
Fail2Ban uses “jails” to define what logs to watch and how to respond.
- Create a new jail:
bash
sudo nano /etc/fail2ban/jail.d/mysqld.local
- Paste this config:
ini
[mysqld-auth]
enabled = true
filter = mysqld-auth
port = 3306
logpath = /var/log/mysql/error.log
maxretry = 5
findtime = 600
bantime = 3600
This means:
- 5 failed attempts in 10 minutes → 1 hour ban.
Step 4: Activate the Filter (If Not Already Available)
- Check for this file:
bash
ls /etc/fail2ban/filter.d/mysqld-auth.conf
If it’s not there, create it:
bash
sudo nano /etc/fail2ban/filter.d/mysqld-auth.conf
Add this:
ini
[Definition]
failregex = Access denied for user .* from '<HOST>'
ignoreregex =
Save and exit.
Step 5: Restart Fail2Ban & Test
bash
sudo systemctl restart fail2ban
Check status:
bash
sudo fail2ban-client status mysqld-auth
You should see:
- Currently banned IPs
- Number of attempts
Monitoring & Management
See all active jails:
bash
sudo fail2ban-client status
Unban an IP:
bash
sudo fail2ban-client set mysqld-auth unbanip YOUR.IP.ADDRESS
Pro Tips for Even Stronger Security
- Use UFW or firewalld to restrict MySQL to trusted IPs.
- Disable remote root login in MySQL:
sql
UPDATE mysql.user SET host='localhost' WHERE user='root';
- Change the MySQL port from 3306 to a non-standard port.
- Set up alerts so you get notified on bans:
ini
action = %(action_mwl)s